Quick Summary
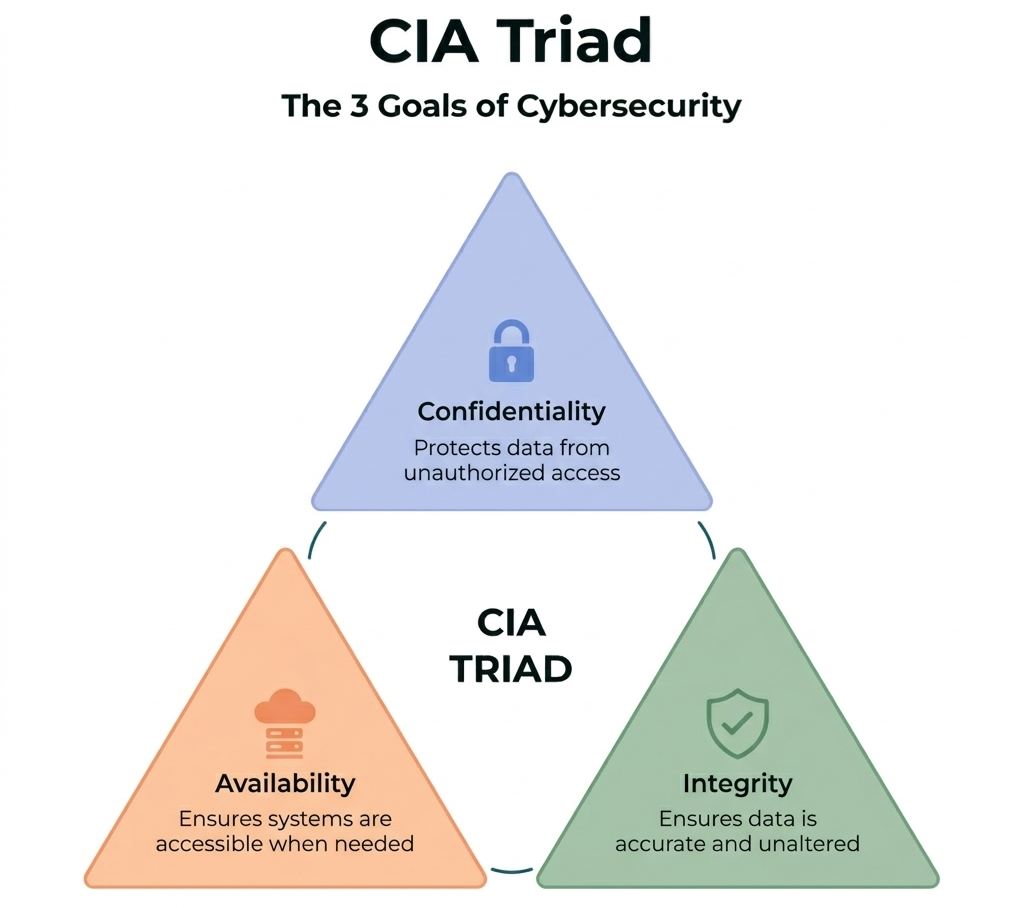
- What it is: The CIA Triad is the foundational cybersecurity framework defining three core goals: Confidentiality, Integrity, and Availability.
- Key fact: CIA stands for Confidentiality which protects data privacy, Integrity which ensures data accuracy, and Availability which guarantees system access.
- Why it matters: Every cybersecurity tool, system, and policy maps back to one of these three principles. Understanding the CIA Triad is the foundation of all security knowledge.
- Best for: Students, beginners, and professionals exploring cybersecurity fundamentals.
What is the CIA Triad?
The CIA Triad in cybersecurity is the most fundamental model for defining what it means for a system or data to be truly secure. CIA stands for Confidentiality, Integrity, and Availability. These are the three principles that every security strategy, tool, and policy is built around.
It breaks down the entire discipline into three focused goals:
- Data should be private (Confidentiality)
- Data should be accurate (Integrity)
- Data should be accessible when needed (Availability)
If even one of these fails, the system is not truly secure.
Why the CIA Triad Matters
Most people think cybersecurity is only about stopping hackers. That is just one part of the picture.
A system can be compromised in three different ways. Unauthorized access breaks confidentiality. Tampered data breaks integrity. Disrupted services break availability. All three cause real damage.
According to IBM's Cost of a Data Breach Report, organizations lose millions every year due to failures in access control, data accuracy, or system uptime. These are not random incidents. They are direct breakdowns of the CIA Triad.
As cybersecurity evolves, technologies like artificial intelligence in cybersecurity are now being used to strengthen confidentiality, integrity, and availability by detecting threats faster and automating responses in real time. Every security control you put in place maps to one of these three goals. That is what makes this model so useful.
The Three Goals of Cybersecurity: CIA Triad Explained
1. Confidentiality: Keeping Data Private
Confidentiality means only authorized people can access specific data. It is the principle behind every login screen, encryption layer, and access policy.
When you check your bank account online, you expect no one else can see your balance. That is confidentiality in action.
How it is achieved:
- Encryption (data is scrambled and unreadable to unauthorized users)
- Multi-factor authentication (more than just a password is required)
- Role-based access control (users only see what their role requires)
- Data classification (labeling data as public, internal, or restricted)
What breaks it: Confidentiality fails when data is breached, passwords are leaked, or someone gains unauthorized access. According to Veeam's 2024 Data Protection Trends Report, 75% of organizations were hit by ransomware in 2023. Many of those attacks exposed sensitive personal and business data.
Real example: A hospital stores patient records in an encrypted database. Only authorized doctors and nurses can open those records. If the encryption is bypassed, confidentiality is broken and patient privacy is at risk.
2. Integrity: Keeping Data Accurate
Integrity means data stays accurate and cannot be changed without authorization. Private data is useless if it can be silently altered.
Imagine a financial system where transaction amounts can be modified without any record. No unauthorized access happened. But the data can no longer be trusted. That is an integrity failure.
How it is achieved:
- Hashing algorithms (a unique fingerprint is created for data; any change alters the fingerprint)
- Digital signatures (confirm who approved or sent the data)
- Checksums (verify that files are not corrupted)
- Version control (track every change made to data over time)
- Audit logs (record who accessed or modified what, and when)
What breaks it: Integrity is violated by data tampering, man-in-the-middle attacks, and malware that silently edits files.
Real example: A government agency publishes official documents online. Each document has a digital signature. If someone changes the file, the signature no longer matches. The tampering is detected immediately.
3. Availability: Keeping Systems Accessible
Availability means systems and data are accessible to authorized users when they need them. A perfectly secure system that is always down is useless.
This is why companies invest in cloud infrastructure, redundant servers, and disaster recovery plans.
How it is achieved:
- Redundant servers and load balancing (traffic is spread so no single server fails)
- Regular backups and disaster recovery plans
- Automatic failover (backup systems activate if the primary one goes down)
- DDoS protection (defends against attacks that flood a system with traffic)
- Real-time monitoring and alerts
What breaks it: Availability is threatened by DDoS attacks, ransomware, hardware failures, power outages, and natural disasters.
Real example: In February 2024, a ransomware attack on Change Healthcare shut down IT systems across hospitals and pharmacies in the United States. Patients could not get prescriptions filled. That was a direct and critical failure of availability.
CIA Triad in Cybersecurity: At a Glance
Real-World Example: An Online Shopping Platform
A single e-commerce website depends on all three pillars at once.
- Confidentiality is at work when your payment details are encrypted at checkout. Only the platform and payment processor can see that data.
- Integrity is at work when your order arrives exactly as you placed it. The item, price, and address are not changed between your click and the seller's screen.
- Availability is at work when the website loads smoothly at 2 AM during a big sale. Redundant servers and load balancing make that possible.
If any one of these fails, user trust breaks down immediately.
Beyond the CIA Triad: How the Model Has Evolved
The CIA Triad has been a cornerstone of information security since the 1970s and 1980s. Its roots go back to early U.S. military computing research.
It remains the most widely used framework in cybersecurity today. But security professionals have developed expanded models to cover gaps it does not address.
One well-known extension is the Parkerian Hexad. It adds three more principles: authenticity (verifying the origin of data), possession or control (ensuring authorized parties keep control of data), and utility (ensuring data is usable in the right format).
Other important concepts include non-repudiation (a person cannot deny having taken an action) and authentication (verifying users are who they claim to be).
These additions build on the CIA Triad. They do not replace it. The three core goals remain the starting point for every security conversation, certification, and framework in the industry.
How to Start a Career in Cybersecurity
Understanding concepts like the CIA Triad is the first step, but building a career in cybersecurity requires going beyond theory.
In real-world roles, these principles are applied across cloud systems, security operations, and threat detection workflows. This is where structured cyber security career path becomes important. Many learners begin by exploring a cyber security course in India to gain hands-on experience with tools, real-world scenarios, and industry practices.
It’s also useful to understand the career side of the field. With growing demand across industries, cybersecurity roles continue to offer strong growth and evolving cybersecurity salary trends based on skills, specialization, and experience.
The key idea is simple. Learning the CIA Triad builds your foundation, but applying it in real systems and understanding the industry is what makes you job-ready.
TL;DR
The CIA Triad in cybersecurity covers three goals: keep data private (Confidentiality), keep data correct (Integrity), and keep systems running (Availability). CIA stands for Confidentiality, Integrity, and Availability. Every security decision in the field connects back to one of these three principles. Understanding the CIA Triad is the foundation of understanding cybersecurity.
FAQs: CIA Triad in Cyber Security
What are the three goals of cybersecurity?
The three goals of cybersecurity are Confidentiality, Integrity, and Availability. Together, they ensure that data is protected from unauthorized access, remains accurate and unaltered, and is available whenever needed.
What do you mean by CIA Triad?
The CIA Triad is a cybersecurity model that defines the three core principles of securing information: keeping data private (confidentiality), maintaining its accuracy (integrity), and ensuring it is accessible (availability). It is the foundation of all security systems.
What is CIA in ITIL?
In ITIL, the CIA Triad is used as part of information security practices to ensure that IT services protect data, maintain its accuracy, and remain reliably accessible for users.
What is the CIA Triad in healthcare?
In healthcare, the CIA Triad helps protect sensitive patient data and medical systems. It ensures that patient records remain private, are not altered incorrectly, and are available to doctors and staff when needed for treatment.
Why is the CIA Triad important?
The CIA Triad is important because it provides a clear framework for designing secure systems. It helps organizations balance data protection, accuracy, and accessibility, which are essential for preventing security breaches and system failures.
Where is the CIA Triad used in real life?
The CIA Triad is used in almost every digital system, including banking, e-commerce, healthcare, and cloud platforms. It guides how data is stored, protected, and accessed in real-world applications.









